The Pujo Question
”Men go to far greater lengths to avoid what they fear than to obtain what they desire.” -- Dan Brown, The Da Vinci Code
On December 19, 1912, a seventy-five-year-old banker sat before Congress and told the most powerful legislative body on earth that the entire financial system ran on something it could not regulate. Samuel Untermyer, lead counsel for the Pujo Committee, had spent weeks building a case that J. Pierpont Morgan controlled American finance through interlocking directorates, syndicate partnerships, and the sheer gravitational mass of capital. Morgan denied it. He argued that if he had any influence at all, it stemmed from one thing only: the faith others placed in him.
Untermyer pressed: “Is not commercial credit based primarily upon money or property?”
Morgan answered: “No sir. The first thing is character.”
“Before money or anything else?”
“Before money or anything else. Money cannot buy it. A man I do not trust could not get money from me on all the bonds in Christendom.”[2]
The exchange was either the most honest testimony in the history of Congressional hearings or the most brazen. Possibly both. Here was a man telling Congress, in public and under oath, that the entire American financial system rested on something that could not be measured, audited, regulated, or taxed. Character. Conviction. The willingness of one human being to believe another. Untermyer had arrived with balance sheets and organizational charts, the tools of a man who believed power resided in structures. Morgan dismissed them with a claim that would have made a philosopher blush: power resided in relationships, and relationships resided in character, and character could not be bought with all the bonds in Christendom. The claim was preposterous. It was also, as the next century of institutional substitutes would demonstrate, more or less correct.
Three months later, Morgan was dead. The Federal Reserve Act, creating the institutional substitute for everything Morgan had done personally, was signed into law the same year. The coincidence is too neat to be satisfying, but the timing captures something real: the moment Morgan died was the moment the country decided that one man’s character was not a sufficient foundation for the world’s largest economy. They were right to decide this. And yet the system they built to replace him has spent the subsequent century trying to solve the problem Morgan identified, and it has not succeeded, because the problem does not have an institutional solution.
Charlie Munger described the alternative with a medical metaphor: “A Mayo operating room is what I call a seamless web of deserved trust. The surgeons trusting the anesthesiologist, the anesthesiologists trusting the surgeon. There’s no bureaucracy at all.”[3] Munger modeled Berkshire Hathaway on the operating room. Twenty-five billion dollars in annual revenue, a corporate staff of fewer than thirty people. The ratio is absurd by any conventional management standard. It worked because bureaucracy is a tax on distrust, and Berkshire had eliminated the tax by selecting, over decades, people who did not require it.
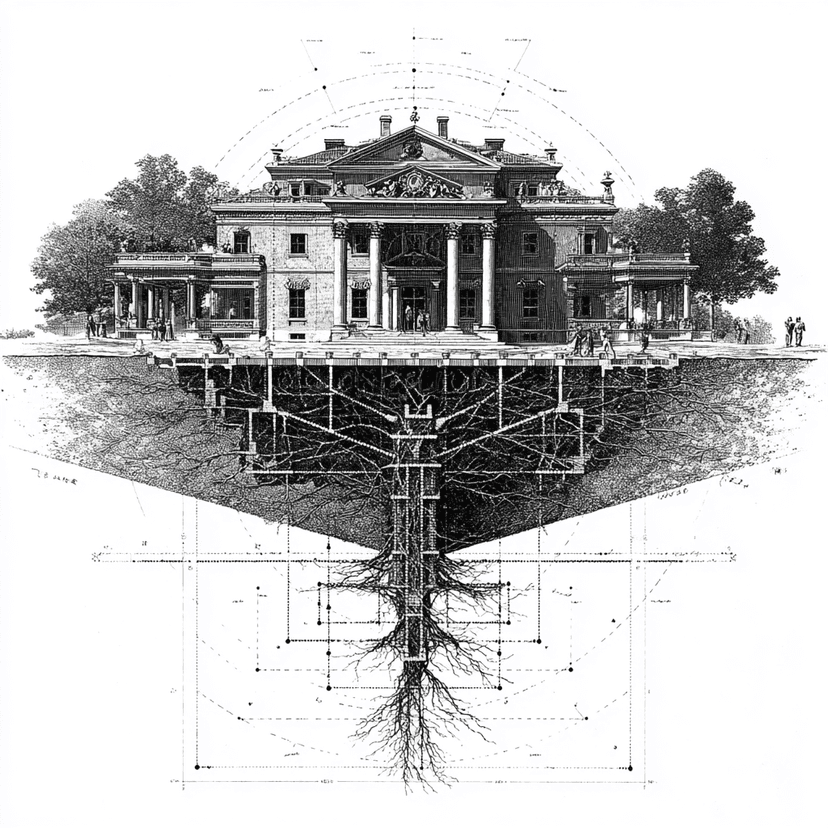
The Morgan Problem is this: trust is the lowest-cost coordination mechanism ever devised, and there is no reliable way to manufacture it, no way to scale it beyond the reach of human relationships, and no way to maintain it once the conditions that produced it change. Every other asset can be managed. Trust can only be earned, and earning it takes decades while losing it takes minutes. This volume traces the architecture of that earning across two thousand years of evidence, from Phoenician temples to Morgan’s library, from Mesmer’s salon to a crushed elevator in an office building, and maps the structural failure modes that destroy these systems whether their operators cooperate or not.
The Borrowed Face
”Credit is a system whereby a person who can not pay gets another person who can not pay to guarantee that he can pay.” -- Charles Dickens
In the 1840s, the phrase “American credit” was an oxymoron in London financial circles. Several states had defaulted on bonds held by British investors. When Maryland commissioners arrived in London to discuss renegotiating their debt, they found no bankers willing to listen. An entire nation’s borrowing capacity had been destroyed by the behavior of a few states, and the damage was collective: the good-faith states suffered alongside the deadbeats because no British investor could distinguish between them at a distance.
George Peabody, a Massachusetts-born merchant who had established himself in London, organized a solution that would set the template for the next century of American finance. He threw a dinner. A dozen of the most important bankers in the City of London, seated around a table, listening to an American they knew personally vouch for Americans they did not. The bankers extended $8 million to Maryland, not because Maryland’s finances had improved, but because Peabody had staked his personal reputation on the creditworthiness of the state. He waived his $60,000 commission on the deal to reinforce the signal: he was not doing this for profit. He was doing it because he believed the debt would be repaid.[1]
The dinner established the operational template for the House of Morgan for the next century. A private individual interposes his personal reputation between a borrower and a lender. The borrower cannot raise capital on its own. The lender will not extend it without a guarantee. The intermediary adds no physical asset to the transaction. He adds his face. The face has a specific economic function: it reduces the lender’s perceived risk to the point where the loan becomes attractive, and it does so at a fraction of the cost of the risk it eliminates. Munger captured the economics: “I’d rather have a brief telephone with somebody I trust than I would a 40-page contract prepared by the finest law firm in the world with somebody I don’t trust.”[3] The telephone call coordinates behavior at near-zero transaction cost. The contract coordinates behavior at enormous transaction cost. The difference in cost is the value of the face.
Peabody’s model was inherited by Junius Morgan, his partner, and then by Junius’s son, J. Pierpont Morgan. For three generations, the House of Morgan operated as a credibility intermediary: a firm whose primary asset was not capital but standing. The capital was necessary. The standing was the business.
The model reached its most dramatic expression on a November evening in 1907, when the presidents of New York’s trust companies arrived at Morgan’s library to discuss a coordinated rescue of the financial system. Morgan observed the gathering and told Benjamin Strong: “When the presidents of the trust companies came into the office they had to be introduced to each other, and I don’t think much can be expected from them.”[2]
Think about that scene for a moment. The men who collectively controlled more money than most sovereign nations had to exchange handshakes like strangers at a cocktail party. Here was a gathering of the most powerful financiers in the Western world, and they needed name tags. The commercial banks, which Morgan had cultivated through decades of personal relationships, had coordinated rescues before. The trust companies, which had grown rapidly outside Morgan’s network, had no history of cooperation and no personal ties between their leaders. In a crisis that required collective action in hours, these men were strangers to each other. Strangers cannot coordinate. Coordination requires history. History requires time that a financial panic does not provide.
Morgan solved the problem the only way it could be solved in the time available: he substituted his own credibility for the credibility the group lacked. He lent them his face. Then he locked the bronze doors of his library at 36th Street and kept them locked until the trust company presidents signed the rescue agreement at 4:45 in the morning. A seventy-year-old man physically imprisoned a room full of bank presidents for an entire night because his personal standing was the only coordination mechanism that worked across institutional boundaries. It was magnificent. It was also, as the next century would demonstrate, completely unsustainable. You cannot build a financial system on the assumption that the right old man will always be available to lock the right door.
The Character Test and Its Failures
”The world is a stage, but the play is badly cast.” -- Oscar Wilde
Morgan’s method for evaluating creditworthiness was social, not financial. Character was measured through proximity: which clubs a man belonged to, which families he married into, which universities he attended, which partners already vouched for him. The method had nothing to do with nepotism disguised as meritocracy. It reflected an explicit belief that social networks revealed character better than balance sheets. The belief had operational logic for decades before it became catastrophic.
A man who belonged to the right clubs had been vetted by the club’s membership committee. A man who married into the right family had been evaluated by the family. A man whom other partners relied on had survived the scrutiny of people whose livelihoods depended on accurate character assessment. The social network functioned as a distributed due-diligence system: each node had performed its own evaluation, and a man who had passed through multiple nodes had been tested by people with real stakes in the outcome. A balance sheet can be fabricated in an afternoon. A network position built over twenty years cannot.
Machiavelli identified the vulnerability five centuries before Morgan exploited the strength. “All men in general judge thereof rather by the sight than by the touch; for every man may come to the sight of him, few come to the touch and feeling of him.”[4] The distinction between sight and touch, between the signal of reputation and the substance of character, is the structural flaw in every system built on social vetting. The Morgan test operated on sight: the clubs, the marriages, the endorsements. The test worked most of the time because sight correlated with touch. But Machiavelli’s point was that few people ever get close enough to verify the substance behind the signal, and those few who do “dare not oppose the opinion of many.”
Ferdinand Pecora was one of the few who dared. In 1933, the son of Sicilian immigrants, a former assistant district attorney from a world the Morgan partners could not have located on a social map, sat across from the most powerful bankers in America and asked them to explain themselves. The Morgan partners arrived at the hearings expecting deference. They received Pecora. When he read the “preferred list” into the public record, the names landed like small detonations: Calvin Coolidge, three thousand shares of Standard Brands. Corporate executives. Politicians. Social luminaries.[1] The preferred list was not bribery in the legal sense. No quid pro quo was specified. But the list functioned as a reciprocity engine: the recipients of Morgan’s generosity felt obligated to Morgan, and the obligation was never explicitly invoked because it never needed to be. A Christmas gift and a below-market stock allocation share the same emotional architecture. The difference is in magnitude, and in how long you can pretend the magnitude does not matter. The system that ran on character was undone by a list of names read aloud by a man the system had been designed to exclude.
Russell Leffingwell, a Morgan partner, argued that any attack on the firm was “an attack on our social order.” The partners had come to believe that their standing functioned as a public good, not just a business asset. Questioning Morgan was questioning civilization. At that point, no evidence of wrongdoing could be processed as evidence, because processing it would require questioning civilization, and civilizations do not update on quarterly earnings reports.
Five years later, the system’s central pillar cracked. Richard Whitney was the president of the New York Stock Exchange, the brother of Morgan partner George Whitney, a member of the most exclusive clubs in New York, a descendant of one of the oldest families in Massachusetts. By every measure that the Morgan system used to evaluate character, Whitney was impeccable. In 1938, he was convicted of embezzlement. He had been stealing from the Exchange’s trust fund and from the estates of friends and relatives for years, conducting a sustained campaign of deception from the position where scrutiny was lowest because the assumption of reliability was highest. The burglar who robs the house next to the police station understands something about human psychology that the homeowner does not.
Here is the uncomfortable detail that the Morgan hagiographers prefer to omit: the mechanical tools to detect Whitney’s fraud existed. Frank Benford had published his law of leading digits that same year, 1938, describing the counterintuitive distribution of first digits in naturally occurring datasets. Fabricated financial data almost never follows Benford’s distribution because humans intuitively assume digits should be evenly distributed. Modern forensic accountants use Benford’s Law as a first-pass screen for fabricated numbers. The Morgan system did not fail because verification tools did not exist. It failed because the system’s ideology held that verification was unnecessary for men of character. The tools were there. The willingness to use them was not. The character test was a way of deciding whom to trust. It was also a way of deciding whom not to verify. These are the same decision, and the second formulation reveals what the first conceals.
Marc Andreessen identified the modern version of this dynamic: “The most high-status people are the most prone to just go along because they’re the most focused on status.”[11] The observation inverts the conventional assumption that elites are independent thinkers. The professor who disagrees with the department risks tenure. The fund manager who bets against the market risks outflows. The banker who questions a colleague’s integrity risks social exclusion. At every level, the cost of questioning rises with status, which means the people best positioned to detect fraud are the people least incentivized to look for it. This is not a bug in the system. It is the system. The same mechanism that makes elite networks valuable (members protect each other’s standing) is the mechanism that makes them blind (members cannot afford to question each other’s standing).
If you work in any organization where someone’s competence is considered above verification, where questioning a particular person’s judgment is treated as a breach of protocol rather than an act of diligence, you are inside the Morgan character test. The question is not whether the person you are not questioning is Whitney. The question is whether you would know if they were.
The Signaling Game
”I will believe it when I see it” is a philosophy for fools. “I will see it when I believe it” is how the world actually works. -- Various, attributed
Michael Ovitz ran Creative Artists Agency for twenty-five years without a written contract with a single client. “In 25 years at CAA, I didn’t have written documents with employees or clients,” Ovitz recalled. “We never lost a client the whole time I was there.”[7] The claim sounds impossible in an industry where betrayal is not a risk but a scheduling conflict. But the claim was true. Ovitz retained clients for decades in a business where the standard retention period was measured in months.
The mechanism was structural, and it ran on a principle that most operators would consider suicidal: the elimination of protection. Under Screen Actors Guild rules, a client who did not work for 91 days had the right to fire their agent regardless of any contract. A written contract gave the client a date to look forward to, a moment when they could evaluate whether to stay or leave. The absence of a contract meant the evaluation was continuous. The client stayed because the agent was delivering. The agent delivered because the client could leave at any moment. The absence of protection produced the performance that made protection unnecessary. Most organizations add contractual armor when they feel vulnerable. Ovitz removed it and discovered that the vulnerability itself was the engine.
Ovitz’s mentor, Herb Allen II, taught him the principle in its most extreme form: “Don’t ask anybody for anything.” Allen’s approach to deal-making was pure contingency: do the work, deliver the result, and only then discuss compensation. When Ovitz approached Sony about acquiring Columbia Pictures, he proposed full contingency. If the deal succeeded, CAA would be paid generously. If it failed, only expenses would be covered. The willingness to work for free until results materialized communicated something that no contract could: the agent believed in his own ability enough to bet his time on it. The bet itself was the credibility-building mechanism.
When Jamie Dimon became CEO of Bank One in 2000, he translated the same principle into a different language. His first move was to put half his personal wealth into Bank One stock. “I was going to be the captain of the ship. I was going to go down with the ship.”[8] Warren Buffett used the identical mechanism when he bought shares in The Washington Post and wrote to Kay Graham that “writing a check separates conviction from conversation.” The check was the signal. The letter was the interpretation of the signal. Together they communicated: I believe in your company enough to risk my capital, and I accept your authority enough to not seek control.
The common architecture across Ovitz, Dimon, and Buffett is what economists call costly signaling: a commitment that is credible precisely because it is expensive to fake. A verbal promise to stay can be revoked at any time. Half your wealth locked in company stock can only be revoked at enormous personal cost. The audience evaluates the commitment by evaluating the cost of faking it, and when the cost of faking is high enough, the commitment is believed.
But here is where the framework turns on itself. Costly signaling explains how credibility is communicated. It does not explain how credibility is built. Dimon’s stock purchase told Bank One employees that his incentives were aligned with theirs. It did not make him competent. It did not make him honest. It made him expensive to distrust. The distinction matters because every great fraud in history has used the same architecture: Bernie Madoff’s consistent returns were a costly signal of competence (who would fake mediocre-looking returns?). Ivar Kreuger’s government loans were a costly signal of legitimacy (who would lend to sovereign nations without real assets?). The signal looked identical to the genuine article because the cost structure was identical. The only difference was that the substance behind the signal was hollow, and the cost of discovering the hollowness was borne not by the signaler but by everyone who believed him.
Signaling is necessary but radically insufficient. It is the visible layer of an architecture that also requires structural foundations, institutional memory, and the willingness to verify what the signals promise. The operators who rely on signals alone are building on sand. The operators who combine signals with structure are building something that might last. The key word is “might.” This volume has no guarantees to offer.
The Architecture of Belief
”The first principle is that you must not fool yourself, and you are the easiest person to fool.” -- Richard Feynman
In 1778, Franz Anton Mesmer arrived in Paris and established a clinic that treated patients through “animal magnetism.” The clinic was an architectural masterpiece of manufactured belief. Richly stained glass. Spacious salons covered with mirrors. In the center of the main room stood the baquet, an oval vessel containing wine bottles filled with magnetized water, iron filings, and glass rods protruding through holes in its iron lid. Mesmer himself appeared “dressed in a long robe of lilac-coloured silk richly embroidered with gold flowers, bearing in his hand a white magnetic rod, and with a look of dignity which would have sat well on an eastern caliph.”[5]
A man in a lilac silk robe, waving a magnetic rod at sick people in a room full of mirrors. The year was 1778, not 1378. Benjamin Franklin was in Paris at the time. The Enlightenment was supposedly in full swing. And yet some of the most educated people in France were paying serious money to sit around a tub of magnetized water while a man in embroidered silk told them their ailments were caused by improperly distributed animal fluids. The scene is comedy. The results were real. Mesmer’s patients felt better after treatment. Not because animal magnetism existed, but because the staging created an expectation of healing that the body’s own mechanisms fulfilled. The architecture of belief did not cure disease. It activated the placebo effect, which is itself a genuine medical phenomenon. The staging was expensive enough to be credible. Cheap staging would not have produced the same expectation. Without the expectation, no placebo. Without the robe, no expectation. The lilac silk was load-bearing.
The principle operates in every domain where belief affects outcomes. The bank that occupies a marble building at a prestigious address inspires more depositor faith than the bank in a strip mall. The faith does not make the bank’s balance sheet stronger, but it makes depositors less likely to withdraw, which makes the balance sheet stronger. Morgan understood this. His office at 23 Wall Street, known as “the Corner,” was the most imposing address in American finance. The building was character made physical. The marble said what Morgan said before Congress: substance first, everything else second. Whether the marble proved the substance or merely asserted it was a question the depositors never needed to ask, because asking it would have been rude, and not asking it was precisely the point.
Three thousand years before Morgan built his marble corner, Phoenician merchants solved the coordination problem at Mediterranean scale. The Phoenicians traded with dozens of civilizations across thousands of miles of coastline. Each transaction occurred between strangers. Each stranger had the incentive to cheat. The Phoenicians built their solution on temples. The temple of Melqart at Tyre guaranteed contracts between merchants and their trading partners. A merchant who defaulted on a temple-guaranteed contract faced not just financial penalty but divine punishment. The combination of physical infrastructure (a neutral location), institutional arbitration (the priesthood), and supernatural enforcement (the gods themselves) created a system that operated across vast distances between parties who had never met.[6] The gods, one suspects, were not consulted about the arrangement. They did not need to be. Their reputation preceded them, which was the entire point.
The Phoenician system worked because it externalized trust from the individual to the institution. Morgan’s system required each party to evaluate the other’s character personally. The Phoenician system required each party to have faith in the temple, and the temple’s standing was maintained by the accumulated weight of thousands of successful transactions and the feared consequences of divine displeasure. The individual merchant did not need to be reliable. The system made him reliable by imposing costs on betrayal that exceeded the gains from cheating.
John Law’s paper bank in 1716 France added a third layer. Law’s invention was to build credibility not by guaranteeing stability but by guaranteeing protection from instability. The French public did not trust the government to maintain the value of its coinage (the government had debased it repeatedly, so the distrust was rational). Law made his bank notes payable in the coin current at the time of issue, not at the time of redemption. The distinction was subtle but transforming: Law’s notes were immune to government manipulation because they locked in the coin value at issuance. “This last was a master-stroke of policy, and immediately rendered his notes more valuable than the precious metals.”[5] The notes were believed not because Law was believed but because the notes were structured to eliminate the specific risk the public feared. The credibility was architectural, embedded in the instrument’s design, rather than personal, dependent on the character of the issuer.
The Law bank succeeded brilliantly until it failed catastrophically. Law expanded from sound banking into stock speculation, creating the Mississippi Company and inflating its shares through a cycle of debt-fueled purchases. The same public that had believed in Law’s notes because they protected against government debasement now believed in Law’s stock because it had gone up. The basis of belief shifted from structural (the design of the notes) to social (the crowd buying the stock). When the crowd reversed, the belief collapsed, and the Mississippi Bubble destroyed France’s willingness to experiment with paper money for seventy years. Law died in poverty in Venice. His bank notes, the ones backed by structural design, had been sound. His stock, backed by crowd sentiment, had been worthless. He could not tell the difference between his two creations, and neither could anyone else, which is the entire problem.
Isaac Newton bought shares in the South Sea Company early in 1720, made money, and sold. The stock kept rising. Newton watched from the sidelines as colleagues and neighbors grew rich. Then he bought back in at a much higher price. The stock collapsed. Newton lost twenty thousand pounds, a sum large enough to devastate even a man of his means. “I can calculate the movements of the heavenly bodies,” he reportedly said, “but I cannot calculate the madness of the people.” His niece Catherine Conduitt recorded that he could not bear to discuss the loss for the rest of his life. A man who had rewritten the laws of physics could not bring himself to articulate what had happened to him in a stock market. The silence is the tell. The shame of social capitulation is different in kind from the shame of intellectual error, because it reveals that the mind you trusted most in the world was overruled by the mind you trusted least: the crowd’s.
Newton’s error was not intellectual. His first decision, to sell, was based on analysis. His second decision, to buy back in, was based on the visible evidence that other intelligent people were making money. Public signals dominate private signals in human cognition because they carry the weight of consensus. The cost of being wrong with the crowd is shared. The cost of being wrong against the crowd is borne alone. Newton could bear the solitude of a laboratory for decades. He could not bear the solitude of watching his neighbors get rich without him for months. The man who invented calculus was undone by the same force that undoes everyone: the human incapacity to remain rational while surrounded by people getting rich irrationally. Every subsequent bubble, from railroads to dot-coms to crypto, has replayed the same script with different costumes. The costumes change. The script does not. Newton would recognize every one of them, and he would fall for every one of them again, and his intelligence would be no protection, because intelligence was never the relevant variable.
The Law episode and the Newton episode, separated by four years and one English Channel, reveal a fragility hierarchy that applies to every trust system in this volume. Structural trust, built into the design of instruments and institutions, is the most durable. Personal trust, built on the character and track record of individuals, is less durable but more responsive. Social trust, built on the behavior of crowds, is the least durable and the most dangerous, because it scales faster than either of the others and collapses faster too. Every financial crisis in history is a story of social trust replacing structural and personal trust and then evaporating when the crowd changes its mind. The crowd always changes its mind. The only variable is the timing.
The Dark Architecture
”The surest way to corrupt a youth is to instruct him to hold in higher esteem those who think alike than those who think differently.” -- Friedrich Nietzsche
Thomas Lamont, the most public-facing partner in the House of Morgan during the 1920s and 1930s, maintained relationships with the governments of Japan and Italy that reveal what happens when relationship-building skills are deployed without a moral compass. When Japan invaded Manchuria in 1931, Lamont, who had been Japan’s most prominent American advocate for a decade, refused to condemn the invasion. He drafted a press release for Japan’s Ministry of Finance, and the release was issued, with only cosmetic changes, as if it were the Japanese government’s own words. Ron Chernow noted that Lamont “seemed oblivious to these grisly developments.”[1] He was not oblivious. He was performing. The two look identical from a distance, which is the point.
The ghost-writing was a betrayal operating in two directions simultaneously. Lamont betrayed American public trust by acting as an undisclosed propagandist for a foreign government. He maintained Japanese trust by delivering the propaganda service his Japanese contacts expected. The dual performance was possible because Lamont’s audiences were separated: the American public did not know he had authored the Japanese statement, and the Japanese government did not care about the American public’s expectations. The intermediary who bridges two networks can exploit the information gap between them, presenting a different face to each audience and maintaining both relationships by telling each what it wants to hear. The strategy works as long as the two audiences never compare notes. In the age of the telegraph, they sometimes did not. In the age of the internet, they always do. Lamont’s playbook is now available only to those operating in domains where the audiences are structurally prevented from communicating, which is fewer domains than most operators believe.
At the University of Chicago in the early twentieth century, the economics faculty knew that monopolies were the dominant policy issue of the era. John D. Rockefeller had endowed the university with millions. The faculty published nothing on the topic for years. No one told them not to publish. No memo was sent. No threats were made. The professors figured out what they could not say by observing who was paying their salaries. The self-censorship was spontaneous, rational, and invisible. Each professor independently concluded that publishing criticism of monopolies would endanger the endowment that funded the university that employed them. The conclusion was probably correct. The conclusion was also never tested because no one was willing to test it. The control was perfect because it was invisible, and it was invisible because it operated through the faculty’s own rational self-interest rather than through any external command. The best censorship is the kind where the censored do not know they are being censored, and the best version of that is the kind where they are censoring themselves and congratulating each other on their independence.
The pattern generalizes to every institution funded by a patron. The think tank funded by an industry will not publish research that threatens the industry. The university endowed by a donor will not pursue scholarship that embarrasses the donor. The journalist employed by a media company will not investigate the company’s advertisers. In each case, the control is exerted not through censorship but through selection: the institution hires people who share the patron’s worldview, and the people who are hired maintain the patron’s worldview because their careers depend on it. The faith between patron and institution is real. The faith between institution and public is compromised, because the institution’s output is shaped by interests the public cannot see. If you consume analysis from any institution that receives funding from parties with a stake in the analysis’s conclusions, you are inside this architecture right now. The question is not whether the analysis is compromised. The question is whether you can identify the direction of the compromise, and the honest answer, almost always, is that you cannot, because the compromise operates precisely by being invisible to its audience.
Charlie Munger named the terminal version of this architecture after Frank Serpico, the New York police officer who was nearly murdered for refusing to participate in the endemic corruption of his department. Munger called it “Serpico Syndrome”: the state of a near-totally corrupt institution in which social proof and incentive alignment make corruption the rational individual choice. “Such corruption was being driven by social proof plus incentives, the combination that creates Serpico Syndrome.”[13]
In 1963, Stanley Milgram demonstrated the other half of the architecture. Sixty-five percent of his participants administered what they believed were lethal electric shocks to strangers when instructed by a single authority figure in a lab coat. No social proof from peers was required. A single figure in a position of authority was sufficient to produce obedience to harmful instructions from strangers who had walked in off the street with no prior conditioning. Serpico Syndrome operates through social proof: everyone is doing it. Milgram demonstrated that authority alone produces the same compliance without any peer reinforcement at all. The combination of both forces, authority setting the direction and social proof among peers reinforcing it, is the full architecture of institutional corruption. Morgan was the authority figure. His character assessment was the standard. The partners’ mutual deference was the social proof. The dual mechanism explains why no one detected Whitney’s fraud despite the fraud operating in plain sight: questioning Whitney meant questioning Morgan’s judgment, which meant questioning every partner who had agreed with Morgan’s judgment. The social cost of that chain of questioning exceeded the social cost of losing money to a thief. So they lost money to a thief.
Serpico Syndrome is the dark twin of Munger’s own seamless web. In the Mayo operating room, social proof runs in the direction of competence: every surgeon observes every other surgeon performing at the highest level, and the observation reinforces the standard. In the corrupt precinct, social proof runs in the direction of corruption: every officer observes every other officer taking bribes, and the observation reinforces the practice. The mechanism is identical. It does not distinguish between virtue and vice. It amplifies whatever direction the group has already chosen. The critical variable is not the mechanism but the initial conditions: who was selected into the group, and what standard was established before the social proof began to operate. Hire saints and social proof will produce a cathedral. Hire thieves and social proof will produce a crime syndicate. The mechanism does not care. It only multiplies.
This is the Morgan Problem stated in its most uncomfortable form. Morgan’s character-based selection produced a network in which social proof pointed toward reliability. The Preferred List was the hinge where the same mechanism crossed from legitimate relationship-maintenance into systematic corruption, with every participant’s involvement reinforcing every other participant’s willingness to accept below-market stock offerings from the most powerful bank in America. The mechanism did not change. The direction changed. And no one inside the network could see the change, because the mechanism that produced their faith in the network was the same mechanism that prevented them from questioning it.
The Compounding Ledger
”Men are moved by two levers only: fear and self-interest.” -- Napoleon Bonaparte
In the late 1970s, Bernie Marcus was looking for a loan to build a new kind of home improvement store. He had been fired from Handy Dan. He had a concept but no capital and a damaged reputation. Rip Fleming, a banker at Security Pacific, said no. Fleming said no three times. Each time, his loan officers rejected the application on standard financial metrics. After the third rejection, Fleming did something that bankers almost never do: he stormed into his CEO’s office, slammed the door, and threw his resignation letter on the desk. “You don’t need a banker. You need a computer. Bernie Marcus and Arthur Blank are good people, and you have turned them down three times.”[9]
The CEO realized that losing Fleming meant losing $400 million in accounts. The loan was approved.
Fleming’s willingness to risk his career was the product of something Marcus had been building for years without calculating the return: total transparency. Marcus told Fleming everything. Every problem. Every opportunity. Every mistake. The contrast with Marcus’s nemesis was vivid: “Sigoloff viewed partners, especially bankers, as idiots to manipulate. His philosophy was keep them in the dark and feed them crap like mushrooms.” Sigoloff’s philosophy is the default mode of most operators, which is worth sitting with for a moment. The instinct to manage information, to present the favorable picture, to share good news eagerly and bad news reluctantly, is so universal that most people do not recognize it as a strategy. It is a strategy. It is the most expensive strategy in business, and the bill arrives decades later, at the worst possible moment, when you need someone to slam a door for you and no one in your life has been given the information that would make them willing.
The transparency strategy is counterintuitive because it includes sharing bad news. The manager who shares only good news signals that bad news exists and is being hidden. The banker knows this. The banker discounts everything the manager says. The discount increases the perceived risk, which increases the interest rate, which increases the cost of capital. Marcus’s transparency eliminated the discount. Fleming did not need to wonder what Marcus was hiding because Marcus was hiding nothing. Over twenty years, the cumulative difference between borrowing with full trust and borrowing under suspicion is the difference between a company that dominates its industry and a company that struggles to finance expansion.
The Fleming episode reveals a broader pattern: trust compounds the way capital does, silently, over long periods, through mechanisms the original investor never anticipated.
When Morgan Guaranty began preparing to open a Japanese branch in the 1970s, the bank’s negotiators stumbled on an asset that no balance sheet recorded and no strategist had planned for. In 1904, Pierpont Morgan’s nephew George had married a geisha named Yuki Kato. George’s family ostracized her. But J.P. Morgan & Co. administered Yuki’s trust fund faithfully through two world wars, a depression, and the complete restructuring of the firm. During World War II, Henry Alexander tracked Yuki down in Cologne, Germany. He gave her not only the accumulated principal but interest on the interest. When Yuki moved to Kyoto after the war, she told her neighbor: “You always must trust the Morgans.”[1]
Seven decades later, that neighbor’s son was a banker. The story of the faithfully administered fund preceded the Morgan negotiators into every meeting. The Japanese financial community already knew the Yuki story. They knew that a Morgan commitment, once made, endured through decades, wars, and corporate transformations. The original act cost the firm almost nothing in financial terms. Henry Alexander tracked down Yuki Kato because the firm had an obligation, and the firm honored its obligations. No one in 1904 or 1945 could have predicted the return. The return came anyway, because standing compounds through mechanisms that the original investor never anticipates. The Yuki fund was the financial equivalent of a message in a bottle that washed ashore seventy years later with compound interest.
In the private equity world, Mark Patricof articulated the compounding principle: “In repeat games with a small universe of players, reputation as a good seller is as valuable as reputation as a good buyer. If your buyers consistently make money, they’ll pay higher prices and move faster on your next deal.” The principle reverses standard negotiation logic. Standard logic says: maximize the price on every transaction. Patricof’s logic says: leave enough on the table that the buyer comes back grateful rather than resentful. The first transaction is a one-shot game. The second through fiftieth transactions are a repeated game. In one-shot games, the rational move is to extract maximum value. In repeated games, the rational move is to build a counterparty who wants to play again. Most operators claim to understand this distinction. Most operators, when the contract is on the table, revert to one-shot behavior. The difference between claiming to play the long game and actually playing it is the difference between Marcus and Sigoloff.
Reed Hastings understood the compounding mechanism at its most granular scale. Thirty years ago, as a young engineer at a startup, he left dirty coffee cups scattered around his desk. A janitor named John cleaned them. One morning Hastings arrived early and found John washing the cups. When he became CEO of Netflix, he made a point of washing his own coffee cups in the company kitchen. The act was visible, deliberate, and repeated. A CEO who gives a speech about teamwork sends a message that costs nothing to send. A CEO who washes coffee cups sends a message that costs something every morning, because it requires performing a task that is below his station, in public, consistently. The daily cost is what makes it believable. Ben Horowitz formalized the same principle for Andreessen Horowitz: he fined partners $10 per minute for being late to meetings with entrepreneurs. The fine was trivial. The behavior it enforced was not. Showing up on time to every meeting with a founder who has no leverage over you communicates respect. Communicating respect builds standing. Building standing compounds.
Peter Kaufman distilled the entire architecture to a single experiment. You are standing in front of an elevator. The door opens. A stranger walks in. You have three choices. Smile and say good morning: ninety-eight percent of the time, the stranger will smile and say good morning back. Scowl and hiss: ninety-eight percent of the time, the stranger will scowl and hiss back. Do nothing: you almost always get nothing back. “Whatever you put out, you get back.”[10] Most people wait for evidence of the other person’s reliability before extending goodwill. The wait produces a stalemate: both parties stand in the elevator saying nothing, each waiting for the other to go first. The act of going first costs nothing and returns warmth ninety-eight percent of the time. The only reason most people do not make the trade is that the vulnerability of going first feels larger than it is. Two percent failure rate. Ninety-eight percent return. Any venture capitalist in the world would take that deal. Most people, standing in an elevator, will not.
In 1980, Robert Axelrod invited game theorists from around the world to submit strategies for a repeated Prisoner’s Dilemma tournament. The winning strategy was the simplest entry in the field: Tit for Tat, submitted by the psychologist Anatol Rapoport. Cooperate on the first move. Then mirror whatever the other player did last. The strategy won not because it was clever but because it was readable. Other players could quickly learn what Tit for Tat would do and adjust to cooperate. The most sophisticated strategies, the ones that tried to exploit opponents through complex conditional logic, finished near the bottom. Rapoport had submitted four lines of code. The game theorists who submitted hundreds of lines were outsmarted by a strategy that a child could have designed. Kaufman’s elevator experiment is Tit for Tat reduced to its smallest possible unit: go first, cooperate, and match what comes back. The insight that outlasted every sophisticated strategy in Axelrod’s tournament is the same insight available to anyone standing in an elevator at 8:47 on a Tuesday morning. Go first.
The Succession Trap
”After me, the deluge.” -- Attributed to Madame de Pompadour (and to every founder who failed to plan succession)
Morgan’s 1895 gold guarantee worked because the financial community believed him. But Morgan was seventy-five when he testified before the Pujo Committee in 1912, and he died three months later. The question his death raised was whether the credibility that resided in one man could survive his departure.
It could not. The House of Morgan continued to operate after Pierpont’s death, but the personal authority that had made the firm uniquely powerful did not transfer to his successors. The firm’s capital transferred. Its relationships transferred, partially. Its operational practices transferred. But the specific quality that had enabled one man to guarantee gold flows, lock bankers in a library, and raise $25 million in twelve minutes, that quality was not heritable, trainable, or transferable. The founder can introduce successors to contacts. The founder cannot transfer the decades of shared experience, mutual vulnerability, and tested reliability that make the contacts believe the founder. The introduction creates access. Only time creates belief. And the successor never has as much time as the founder had, because the founder started building before anyone was watching, and the successor starts building under the full weight of comparison.
The Romans had a word for this: dignitas. Public standing. Honor. Reputation as property. A Roman patrician’s dignitas could be accumulated through decades of service, spent carefully to secure favors, defended in court at enormous expense, and inherited by his son, though the inheritance depreciated with each generation that failed to replenish it. Modern “brand management” and “reputation risk” language obscures what the Romans were honest about: elite groups across millennia treat social capital as property requiring active stewardship, not as a byproduct of success. The Roman senator who neglected his dignitas was as reckless as the farmer who neglected his fields. The difference is that the farmer knew when his fields were dying. The senator, surrounded by flatterers, often did not.
Japan’s Ise Grand Shrine offers the only known counter-model. Since 690 AD, the shrine has been dismantled and rebuilt identically every twenty years. The rebuilding is not structural necessity; the cypress could last much longer. The rebuilding exists to transfer the knowledge of how to build the shrine from one generation of carpenters to the next. The physical structure is the pretext. The real product is the continuous transmission of craft. Every twenty years, a new generation of builders constructs the shrine alongside the old generation, learning by doing what cannot be transmitted by instruction. The shrine has been rebuilt over sixty times. The knowledge has never been lost, because the knowledge was never allowed to reside in a single generation.
Morgan’s partners could not replicate this model because relational capital cannot be rebuilt on a twenty-year cycle the way a shrine can. But the Ise model suggests what a deliberate succession architecture might look like: not the transfer of the asset itself, but the continuous practice of rebuilding the asset from scratch so that the knowledge of how to build it never resides in only one person. The firms that survive their founders are the firms that treat relationship-building as a transmissible craft, practiced jointly by the old guard and the new, rather than as a personal gift that dies with the gifted.
The American financial system’s response to Morgan’s death was to build institutional substitutes for personal authority. The Federal Reserve, created in 1913, institutionalized the lender-of-last-resort function that Morgan had performed personally in 1907. The SEC, created in 1934, institutionalized the information-verification function that Morgan’s character test had performed informally. Each institution was less effective than Morgan at his peak and more reliable than Morgan at his weakest. The institutions traded performance for durability: they could not match one singular individual’s capacity for crisis management, but they could operate continuously regardless of any individual’s presence or absence. The mediocre consistency of institutions outperforms the brilliant inconsistency of individuals across any time horizon longer than one man’s career. This is depressing. It is also the foundation of modern civilization.
In August 1991, Warren Buffett received a phone call that would test this thesis more severely than any investment he had ever made. Salomon Brothers, in which Berkshire Hathaway held a major stake, had been caught submitting false bids in Treasury auctions. The fraud was committed by a single trader, Paul Mozer, but the cover-up implicated senior management who had known about the violations for months without reporting them. Buffett flew to New York and took over as interim chairman. His first public statement became Morgan’s character thesis translated into modern corporate governance: lose money and I will be understanding; lose reputation and I will be ruthless.[15]
But Buffett’s situation revealed something Morgan never faced: the trapped steward problem. Buffett had invested in Salomon as a passive holder. He had no operational control over the trading desk. He had not selected the people who committed the fraud. And yet his own standing was hostage to their behavior because the market could not distinguish between Buffett’s judgment in making the investment and Salomon’s ethics in conducting its business. Schroeder wrote that Buffett recognized “with a sickening jolt that investing in Salomon, a business with problems over which he had essentially no control, had put his reputation at risk.” The Morgan Problem in its purest modern form: your standing is your most valuable asset, and you cannot fully control it because it is shaped by the behavior of people you have chosen to rely on.
Lee, Higginson & Co. learned this lesson at terminal cost. The firm had been one of the most prestigious banks in America, a pillar of Boston’s financial establishment. It destroyed itself by placing complete faith in a single client: Ivar Kreuger, the Swedish Match King. After Kreuger committed suicide in Paris in March 1932, the truth emerged. The entire empire was a fabrication. Forged Italian government bonds, phantom companies, manipulated balance sheets. Lee, Higginson admitted that the firm “had taken his word with regard to his holdings and had not investigated the actual state of affairs of his company because of their confidence in his reputation and integrity.”[12] They had acted on Morgan’s principle with total commitment: character first, verification never. The faith itself became the vulnerability. The firm’s belief in its own character-reading ability prevented it from performing the mechanical due diligence that would have revealed the fraud. They trusted their judgment about a man more than they trusted arithmetic about his balance sheet, and the arithmetic was right.
The Kreuger collapse and the Whitney conviction, occurring within six years of each other, demolished both pillars of the Morgan system. Whitney proved that social vetting could miss a fraud at the center of the network. Kreuger proved that character assessment could substitute dangerously for financial verification. Together they demonstrated that faith without verification is a wager, and the Morgan system had been making that wager for decades without knowing it, protected by the statistical likelihood that most members of elite networks were, in fact, reliable. The statistics held until they didn’t. Statistics always hold until they don’t. That is the nature of statistics.
The Formalization Paradox
”In any bureaucracy, the people devoted to the benefit of the bureaucracy itself always get in control and those dedicated to the goals the bureaucracy is supposed to accomplish have less and less influence, and sometimes are eliminated entirely.” -- Jerry Pournelle, Pournelle’s Iron Law of Bureaucracy
In 1889, Andrew Carnegie and the Amalgamated Association of Iron and Steel Workers signed a contract that solved the trust problem between labor and capital through architectural design. Workers’ wages would rise and fall with the market price of steel billets. The contract specified that “the weekly quotations in the market column of the American Manufacturer shall be accepted as the selling prices.”[14] By outsourcing the price determination to a third-party publication, Carnegie created a neutral reference point that neither side could manipulate. The workers did not need to believe Carnegie’s accounting. Carnegie did not need to believe the workers’ claims about market conditions. Both relied on the American Manufacturer because the publication had no stake in the outcome. The underlying principle is the same one that powered the Phoenician temples: when personal trust is insufficient, institutional trust must substitute, and institutional trust is most effective when the institution has no incentive to favor either party.
The sliding scale collapsed in 1892 because Carnegie’s partner Henry Clay Frick changed the terms. Frick proposed lowering the minimum wage floor and shifting the base price downward. The workers saw the renegotiation as a betrayal: the neutral mechanism that had aligned their interests with management was being weaponized against them. The Homestead Strike that followed destroyed the union and cost twelve lives. The architecture that had worked for three years was undone not by a flaw in the design but by one party’s decision to exploit the design for his own advantage. Carnegie, naturally, was on vacation in Scotland. Thirty-five miles from the nearest telegraph. Fishing.
The lesson generalizes: trust architectures are only as durable as the parties’ commitment to honoring them. A neutral mechanism can be corrupted by a powerful actor who decides that neutrality no longer serves his interests. The architecture does not enforce itself. People enforce the architecture, and people can choose to stop.
Before Glass-Steagall and the Securities Exchange Act, the American financial system was regulated primarily by private banking networks. Partner reputation within the network constrained behavior more effectively than any external regulation, because network exclusion meant professional death. A banker who defaulted on an obligation to another member of the network would never raise capital again. The social cost of defection exceeded the financial gain from any single fraudulent transaction.
After the Pecora Hearings, the government replaced the private network with formal regulation. The replacement was necessary. The Whitney scandal had demonstrated that the network’s screening criteria were insufficient. But the replacement had an unintended consequence that Munger later identified: formalization lowers standards. Under the private network, the relevant standard was “would the other members of the network vouch for me?” The standard was high because the social cost of failing it was total exclusion. Under formal regulation, the relevant standard became “am I in compliance with the law?” The standard was lower because the legal cost of failing it was a fine or a prosecution, both of which were survivable. The network enforced standards above the legal minimum because the network’s punishment (social death) exceeded the law’s punishment (financial penalty). When the network was replaced, the effective standard dropped from “reliable” to “legal.” The gap between those two words is where most of modern business ethics lives, uncomfortably, pretending the gap does not exist.
Boeing demonstrated the cost of that gap in the twenty-first century. Before the 1997 merger with McDonnell Douglas, Boeing operated on something close to Morgan’s character system. Engineers trusted engineers. Reputation within the engineering community constrained behavior more effectively than any compliance manual, because a Boeing engineer who cut corners on airframe safety would never work in aerospace again. The merger replaced engineering culture with financial culture: quarterly targets, cost-per-unit metrics, executive compensation tied to stock price. The FAA, in a regulatory arrangement that should have been recognized as structurally insane, delegated aircraft certification authority to Boeing itself. The regulator trusted the regulated. The 737 MAX crisis, which killed 346 people in two crashes, was not a failure of engineering. It was a failure of the trust architecture. Boeing’s engineers knew the MCAS system was dangerous. The compliance framework said the system met regulatory standards. The engineers were right. The compliance framework was legal. And “legal” is not the same as “safe,” for exactly the reason Munger identified: formalization sets a ceiling that becomes a floor. The firm met the regulation and considered itself virtuous for having done so. The people on Lion Air Flight 610 and Ethiopian Airlines Flight 302 paid the price of that virtue.
The pattern recurs whenever informal trust systems are replaced by formal regulatory systems. The informal system enforces higher standards because the punishment for violation is social, total, and immediate. The formal system enforces lower standards because the punishment is legal, partial, and delayed. The informal system’s weakness is that it screens imperfectly (Whitney). The formal system’s weakness is that it sets a ceiling that becomes a floor. In 1989, the Las Vegas Metropolitan Police Department discovered the same dynamic in criminal investigation. Sheriff Kevin McMahill explained: “When somebody is murdered, there’s always somebody who knows who did it. They just don’t talk to the police. But they talk to us because we’re part of the community.” Authority produces compliance. Relationship produces information. The gap between minimum compliance and maximum cooperation is the trust premium, and no regulatory system has ever captured it. Regulators can compel obedience. They cannot compel loyalty. The difference between obedience and loyalty is the difference between a system that survives stress and a system that collapses the moment the enforcer looks away.
This is the paradox the volume cannot resolve: the Morgan system was better and more fragile. The institutional system is worse and more durable. The Morgan system produced higher standards but could not survive the failure of its screening criteria. The institutional system produces lower standards but survives individual failures because no individual is load-bearing. The ideal would be a system that combines Morgan-level performance with institutional durability, and no civilization in the historical record has built one. The Phoenicians came closest, combining personal trading relationships with temple-guaranteed enforcement. The system lasted centuries. Nassim Taleb’s formulation of the Lindy Effect suggests this longevity is itself evidence: the life expectancy of a non-perishable system is proportional to its current age, and the Phoenician model had survived more stress tests than any successor. It did not survive Rome. Nothing survives Rome except the idea that something should.
The Velocity Exception
”Move fast and break things. Unless you are breaking stuff, you are not moving fast enough.” -- Mark Zuckerberg, 2012 (later quietly retired as a motto)
It would be dishonest to close the analytical sections without acknowledging the counter-case: operators who rejected the trust architecture entirely and succeeded, at least for a time, by replacing relational capital with pure transactional velocity.
Travis Kalanick built Uber on the explicit rejection of every principle in this volume. He did not cultivate relationships with regulators; he declared war on them. He did not build trust with drivers; he treated them as interchangeable inputs to an algorithm. He did not invest in the standing of his brand with the public; he subsidized rides below cost and dared the market to look away from the burn rate. The strategy worked, spectacularly, for the better part of a decade. Uber reached a valuation of $68 billion before it went public. It reshaped urban transportation worldwide. It did all of this without anything resembling the Morgan architecture, without personal relationships between the operator and his stakeholders, without reputational capital accumulated over decades, without the slow compounding that this volume has spent nine sections documenting.
The question the Kalanick case forces is whether the trust architecture is actually necessary, or whether it is a luxury that operators with sufficient velocity can skip entirely.
The answer arrived in 2017. When a cascade of scandals hit Uber, from workplace harassment reports to the revelation that the company had built software specifically to evade law enforcement, Kalanick discovered what Morgan could have told him: you do not need relational capital until you need relational capital, and when you need it, you need it immediately, and it cannot be manufactured on demand. No regulator extended goodwill. No driver organization offered support. No board member risked personal standing to defend the CEO. The investors who had funded the growth demanded Kalanick’s resignation with the same transactional efficiency he had applied to everyone else. He was removed from his own company by the logic he had built the company on: pure value extraction, no relational surplus, no loyalty earned and therefore no loyalty extended.
Dov Charney at American Apparel ran the same experiment to an even more destructive conclusion. Charney built a billion-dollar apparel company on speed, provocation, and the deliberate refusal to invest in any relationship that could not be measured in next quarter’s revenue. When the scandals arrived, he discovered the same absence: no reservoir of goodwill, no partner willing to slam a door, no banker willing to throw a resignation letter. The company filed for bankruptcy. Charney was expelled from the firm he had founded. The speed that had built the company had also ensured that nothing durable had been built alongside it.
The Kalanick and Charney cases do not disprove the Morgan architecture. They reveal its negative space: what happens when the architecture is absent. The trust architecture is invisible during growth because growth covers everything. The architecture becomes visible only in the failure state, when the operator needs something that cannot be purchased at market rates: discretion, loyalty, the willingness of a counterparty to absorb cost on your behalf because the relationship is worth more than the transaction. These qualities cannot be manufactured in a crisis. They are either present because they were built over years, or they are absent because they were never built. There is no middle ground and there is no shortcut.
The Portable Playbook
”Distrust all in whom the impulse to punish is powerful.” -- Friedrich Nietzsche
The standard business advice on trust-building sounds like this: be authentic, follow through on commitments, communicate transparently, build relationships before you need them. The advice is accurate in the way that telling a drowning person to swim is accurate. It describes the desired outcome and says nothing about the mechanism.
The evidence in this volume suggests that the advice is aimed at the wrong level entirely. The Morgan partners were not unreliable men. They were reliable within their own network and catastrophically blind to the network’s failure modes. Carnegie was not a poor communicator. He wrote the most eloquent essays on labor dignity in the Gilded Age and then broke a union. Lee, Higginson did not lack commitment to their clients. Their commitment was so total that it prevented them from performing basic financial verification. Kalanick did not lack energy or ambition. He lacked any structure that would survive the moment when energy and ambition stopped being sufficient. The tools the standard advice prescribes are the tools that already failed. What the historical evidence actually supports, from Peabody through Munger, from the Phoenician temples through the Federal Reserve, are structural practices: interventions that operate on the system rather than the individual, that reveal weaknesses in the architecture whether the operator cooperates or not. The three practices below are derived from the specific cases in this volume. They are not adaptable to a generic business book because they depend on the mechanisms documented here. They are thinking tools, not to-do items. The distinction matters because to-do items change your calendar. Thinking tools change the questions you ask.
The Fleming Inversion: A Practice for Pricing Silence
Bernie Marcus built a banker willing to bet his career on a loan application, and the method was years of total transparency including bad news. Most operators understand this story as a lesson about honesty. It is not. It is a lesson about pricing.
Every relationship has an information asymmetry, and the party with less information prices the gap. When Marcus told Fleming everything, including the problems, Fleming could price Marcus’s risk accurately. When Sigoloff withheld information and managed perceptions, his bankers could not price Sigoloff’s risk accurately and therefore overpriced it. The overpricing manifested as restrictive covenants, higher interest rates, shorter terms, and the kind of arm’s-length treatment that makes every negotiation feel like a hostage exchange.
The Fleming Inversion takes this mechanism and makes it operational. First, identify the most important partner relationship in your business, the one where the other party’s cooperation is most critical to your survival. Second, identify the worst piece of information in your current situation, the number you would least like this partner to see, the problem you have been managing quietly because sharing it would invite scrutiny. Third, share it. Not during a crisis, when disclosure looks like desperation. Not in the annual review, when it looks like a footnote. Now, when it looks like conviction.
The reason this works is not that your partner will admire your character. The reason it works is that the partner already knows something is being withheld. Partners always know. They may not know what you are hiding, but they know you are hiding something, because everyone hides something, and the hiding is being priced into every term of every interaction. Fleming’s loan officers evaluated Marcus on the numbers and said no. Fleming, who knew the full picture because Marcus had given him the full picture for years, evaluated Marcus on judgment and character and said yes. The information asymmetry between the loan officers and Fleming was the transparency premium, and it was large enough to override three formal rejections.
The diagnostic is blunt: does the most important financial partner in your business know the worst number in your current situation? If not, they are pricing your silence into every term sheet, and you are paying for the comfort of concealment in ways you cannot see. The comfort is real. The cost is also real. And the cost compounds, because every quarter of silence widens the gap between what the partner knows and what the partner suspects, and the suspicion always costs more than the truth would have.
The harder version of this practice, the one that separates structural thinking from self-help, is to apply it preemptively. Do not wait until you have bad news to share bad news. Build the channel before you need it. Tell your most important partner, this quarter, something uncomfortable that you did not have to share. The uncomfortable thing does not need to be catastrophic. It needs to be real. The partner will remember that you shared it voluntarily. The next time something catastrophic happens, the channel will already exist. Marcus did not build Fleming’s loyalty in a crisis. He built it over years of peacetime disclosure, so that when the crisis came, Fleming already had the information and the relationship required to slam a door. You cannot build the channel during the flood. You build it during the drought, when building it feels unnecessary, which is exactly why most people never build it.
The Sliding Scale Audit: A Practice for Testing Neutral Architecture
Carnegie’s 1889 wage contract is the most elegant trust-building mechanism in this volume, and its destruction is the most instructive failure. The contract worked because it externalized the disputed variable (the market price of steel) to a third party (the American Manufacturer trade publication) that neither labor nor management could manipulate. For three years, the sliding scale eliminated the need for each side to trust the other’s reporting. Both relied on the same neutral reference point. The architecture was beautiful. Frick destroyed it by changing the terms when the power balance shifted in management’s favor.
The Sliding Scale Audit is the practice of identifying every neutral reference point in your most important relationships and stress-testing each one for the same vulnerability that destroyed Carnegie’s contract. The practice has three steps, and the third is the one that matters.
Step one: inventory the neutral mechanisms. In any recurring relationship where both parties have an incentive to dispute the facts, list every reference point that both parties rely on. In a vendor relationship, this might be the SLA metrics, the quality benchmarks, the pricing index. In a partnership, it might be the revenue-sharing formula, the customer satisfaction score, the financial audit. In an investor relationship, it might be the independent valuation, the board-approved budget, the reporting cadence. Most operators can complete this inventory in an hour. Most operators have never done it, because the mechanisms feel stable and stable things do not attract attention.
Step two: for each mechanism, identify the controller. Who sets the terms of the reference point? Who defines the methodology? Who selects the third party? In Carnegie’s contract, the reference point was neutral (a trade publication), but the interpretation of the reference point was controlled by management (Frick redefined the base price). The mechanism looked neutral. The surrounding architecture was not. Most neutral mechanisms have the same structural flaw: the reference point itself is independent, but the terms governing how the reference point is applied are controlled by the stronger party. The independent appraiser values the property, but the bank selects the appraiser. The financial audit verifies the numbers, but the company selects the auditor. The customer satisfaction score measures quality, but the vendor defines which customers are surveyed. Each of these looks neutral from a distance. None of them is neutral under pressure.
Step three, the one that changes the practice from an inventory to a diagnostic: for each reference point, ask what it would cost the stronger party to manipulate it, and whether that cost is high enough to deter manipulation under the specific conditions that would make manipulation attractive. The conditions matter. Frick did not manipulate the sliding scale during prosperous years when steel prices were high and workers were earning well. He manipulated it during a downturn when he had the leverage to impose new terms and the economic incentive to reduce labor costs. The vulnerability lay in the conditions under which the mechanism would be tested, not in the mechanism itself. Every neutral architecture is designed during peacetime, when both parties are cooperative and the incentive to manipulate is low. Every neutral architecture is tested during wartime, when one party is desperate and the incentive to manipulate is existential. Boeing’s certification arrangement looked neutral during normal operations. Under pressure to deliver the 737 MAX on schedule, the arrangement revealed that the regulator had delegated authority to the party with the strongest incentive to abuse it. The architecture was tested by exactly the conditions it was designed to prevent, and the architecture failed because no one had asked, during peacetime, what would happen when wartime arrived.
The audit, applied annually to the two or three most important structural relationships in your business, produces a map of the mechanisms you are relying on and the conditions under which each mechanism would fail. The map does not prevent the failure. It tells you where to look when the conditions change. Most operators discover their neutral mechanisms are compromised only after the manipulation has occurred. The Sliding Scale Audit discovers them before, which is the difference between repair and prevention, and prevention costs a fraction of what repair costs.
The Serpico Pre-Mortem: A Practice for Diagnosing Invisible Drift
Munger’s Serpico Syndrome describes the terminal state: an institution so corrupted that social proof and incentive alignment make corruption the rational individual choice. Milgram demonstrated the adjacent force: authority alone, without any social proof, produces compliance with harmful instructions from sixty-five percent of participants. The combination of both forces is the full architecture of institutional decay. By the time you can identify the terminal state from inside the institution, it is too late. The officers who recognized the corruption in Serpico’s precinct were isolated, threatened, and eventually shot. The practice derived from these frameworks is not a cure for terminal corruption. It is an early-detection system for the drift that precedes it.
The drift has a consistent signature across every institution documented in this volume. It begins not with fraud or venality but with a single tolerated deviation from stated standards. At Morgan, the tolerated deviation was the Preferred List: the practice of offering below-market stock allocations to friends of the firm. The practice was not illegal. It was not, by the standards of the era, unusual. It was simply a gap between the firm’s stated standard (“we evaluate all clients on character alone”) and its actual behavior (“friends of the firm receive preferential financial treatment”). The gap was tolerated because everyone benefited from it. The tolerance of the gap normalized it. The normalization expanded it. Within a decade, the Preferred List included a former president, and the partners could not see the corruption because the corruption was the standard by which they measured normalcy.
The Serpico Pre-Mortem operates on the gap, not the corruption. The practice is conducted quarterly, ideally by someone who is new enough to the organization to still see the gaps that veterans have stopped seeing. The process has four steps.
First, state the organization’s declared standards. Not the aspirational values posted in the lobby. The operational standards that govern daily behavior. “We respond to client emails within 24 hours.” “We promote based on performance, not tenure.” “We make investment decisions based on data, not relationships.” Write them down. Be specific. If the organization cannot articulate its operational standards in concrete, testable terms, that is the first finding.
Second, identify the tolerated deviations. For each standard, ask: where does the organization routinely deviate from this standard without consequence? The client whose emails are never answered within 24 hours because the client is too small to matter. The employee who was promoted despite mediocre performance because the employee is the CEO’s protege. The investment that was approved despite weak data because the recommending partner had a relationship with the founder. These deviations are not hidden. Everyone in the organization knows about them. They are simply not discussed, because discussing them would require confronting someone whose status makes confrontation expensive.
Third, trace the incentive structure behind each tolerated deviation. Who benefits from the deviation? Whose status depends on the deviation continuing? In the Morgan Preferred List, the beneficiaries were the firm’s most powerful partners and their most politically connected friends. The incentive to tolerate the deviation was social: partners who questioned the list questioned the partners who maintained it, and questioning powerful partners had career consequences. In the Chicago economics department, the beneficiary was the endowment, and the beneficiary of the endowment was every professor’s salary. The incentive to tolerate the self-censorship was economic: questioning Rockefeller’s influence meant questioning the funding that paid for the questioning. In both cases, the incentive structure made the deviation rational for every individual participant, even though the deviation was corrosive to the institution’s stated purpose.
Fourth, ask the question that the Serpico Pre-Mortem exists to force into the open: if this tolerated deviation were reported on the front page of the Wall Street Journal tomorrow, would we defend it or deny it? The test is not whether the deviation is illegal. The test is whether the organization would be willing to own it publicly. If the answer is “we would deny it” or “we would explain it away,” the deviation has already drifted past the point where it can be corrected painlessly. The cost of correction is rising with each quarter of tolerance. The cost of discovery, which is the cost of correction plus the cost of the appearance that the organization tolerated the deviation knowingly, is rising faster.
The Serpico Pre-Mortem does not prevent corruption. No practice can prevent corruption when the incentive structure rewards it sufficiently. What the practice does is compress the detection window: the period between when the drift begins and when someone in the organization names it aloud. At Morgan, the detection window was decades. The Preferred List operated for years before the Pecora Hearings forced public disclosure. At the University of Chicago, the detection window was even longer: the self-censorship persisted for a generation. The Pre-Mortem, conducted quarterly with honest participants, compresses the window to months. The drift still occurs. The drift is identified before it becomes the standard by which normalcy is measured. And the distance between early detection and late detection is the distance between a correctable deviation and a structural crisis.
The Line You Cannot See
”We are what we pretend to be, so we must be careful about what we pretend to be.” -- Kurt Vonnegut, Mother Night
It would be satisfying to end with three structural practices and the implication that applying them will produce durable trust. But the Morgan Problem has one more property that this volume cannot afford to ignore: the operators who understood trust most deeply were often the operators who were destroyed by it.
Morgan understood that character was the foundation of credit. He built the most powerful financial institution in the Western world on that understanding. The understanding did not prevent his character test from becoming a mechanism of social exclusion that could not detect a fraud at its own center. Carnegie understood that trust between labor and capital required neutral architecture. He built the most elegant wage contract in American industrial history. The understanding did not prevent his partner from weaponizing the architecture against the workers it was designed to protect. Lee, Higginson understood that character assessment required close personal knowledge of the client. They cultivated that knowledge with Kreuger for years. The understanding did not prevent them from substituting faith for verification until the substitution killed the firm. Kalanick understood none of these things. He built without architecture. The building rose fast and fell faster.
Knowledge of the architecture does not confer immunity from its failure modes. This is the identity loop applied to trust itself: the operator who has spent decades building reliable relationships develops a self-image as a judge of character, and the self-image becomes a barrier to performing the verification that would reveal when the judgment has failed. Morgan’s partners could not verify Whitney because verifying Whitney would have required questioning their own capacity to evaluate character, and their capacity to evaluate character was the foundation of the firm’s existence. The verification would have threatened the identity. The identity prevented the verification. The loop sealed itself.
Kaufman’s elevator experiment offers the only instruction that survives the analysis intact: go first. Smile. Say good morning. Whatever you put out, you get back. The instruction is trivially simple, which is probably why it works. It operates below the level where the identity loop can corrupt it. You do not need to understand signaling theory to smile at a stranger. You do not need to have read this volume. You need only the willingness to extend goodwill before it has been earned, knowing that the extension is a bet, and knowing that the bet pays off ninety-eight percent of the time, and knowing that the two percent of the time it does not pay off is the cost of participating in the only coordination mechanism that has worked for the full span of recorded human history.
Morgan was right. Character first. Before money or anything else. He was also wrong, because character cannot be read from the outside with the reliability his system required, and the faith that character assessment produces can become the very thing that prevents the assessment from being questioned. Both of these things are true simultaneously. The willingness to hold them both, to build trust architectures while suspecting that every trust architecture contains the seeds of its own failure, is not a comfortable intellectual position. It is, however, the only honest one.
On a November evening in 1907, Morgan locked the bronze doors of his library and kept a room full of bankers trapped inside until they agreed to save the financial system. The act was personal, dramatic, and unrepeatable. The institution that replaced him does not lock doors. It adjusts interest rates. The adjustment is more reliable. It is also less human, less dramatic, and less capable of producing the kind of collective commitment that Morgan extracted from a room full of strangers at 4:45 in the morning. We have replaced the locked doors with adjustable rates, and the rates work better than the doors ever did. Something was lost in the replacement that no rate adjustment can recover, and the loss is the cost of the civilization we chose over the one Morgan offered. Whether the trade was worth it is a question this volume leaves with you.
The invisible architecture begins not with institutions, regulations, or contracts but with one person’s willingness to extend faith before it has been earned. The willingness is the foundation. Everything else is structure built on top of it. The structure can fail. Build it anyway.